TCP OS Spoofing (Anti TCP/OS Fingerprinting)
Some websites and anti-bot systems try to detect proxies by comparing your browser's User-Agent (what OS your browser says it is) with the Operating System fingerprint that leaks from low-level TCP/IP behavior. If these two don’t match (for example, browser says
Windows but TCP looks like Linux), your traffic can be flagged as coming from a proxy.
Availability: TCP OS Spoofing is available from the Premium plan.
What is TCP/OS Fingerprinting?
- Idea: Each OS/network stack (Linux, Windows, macOS, Android, etc.) handles TCP/IP slightly differently.
- Result: Sites can infer your OS by inspecting TCP options, window sizes, TTL, MSS, timestamps, etc.
- Detection: If your browser fingerprint says “Windows 10” but TCP looks like “Linux,” it’s abnormal.
Why OS Spoofing matters
- Most proxies run on Linux. If you use a Windows browser profile through a Linux proxy, it may look suspicious.
- OS Spoofing adjusts the proxy’s TCP/IP signature to imitate another OS (e.g., Windows), aligning it with your browser profile.
- Goal: Reduce proxy detection and improve trust on strict websites.
When should you enable it?
- Using Windows-based browser profiles (e.g., in antidetect browsers) while your proxy server is Linux.
- Sites complain about “Proxy/VPN detected” or show inconsistent environment/OS warnings.
- Testing on sites that check TCP/OS fingerprints (see below).
Supported OS fingerprints
- Windows
- Android
- Linux (default)
- iOS
- macOS
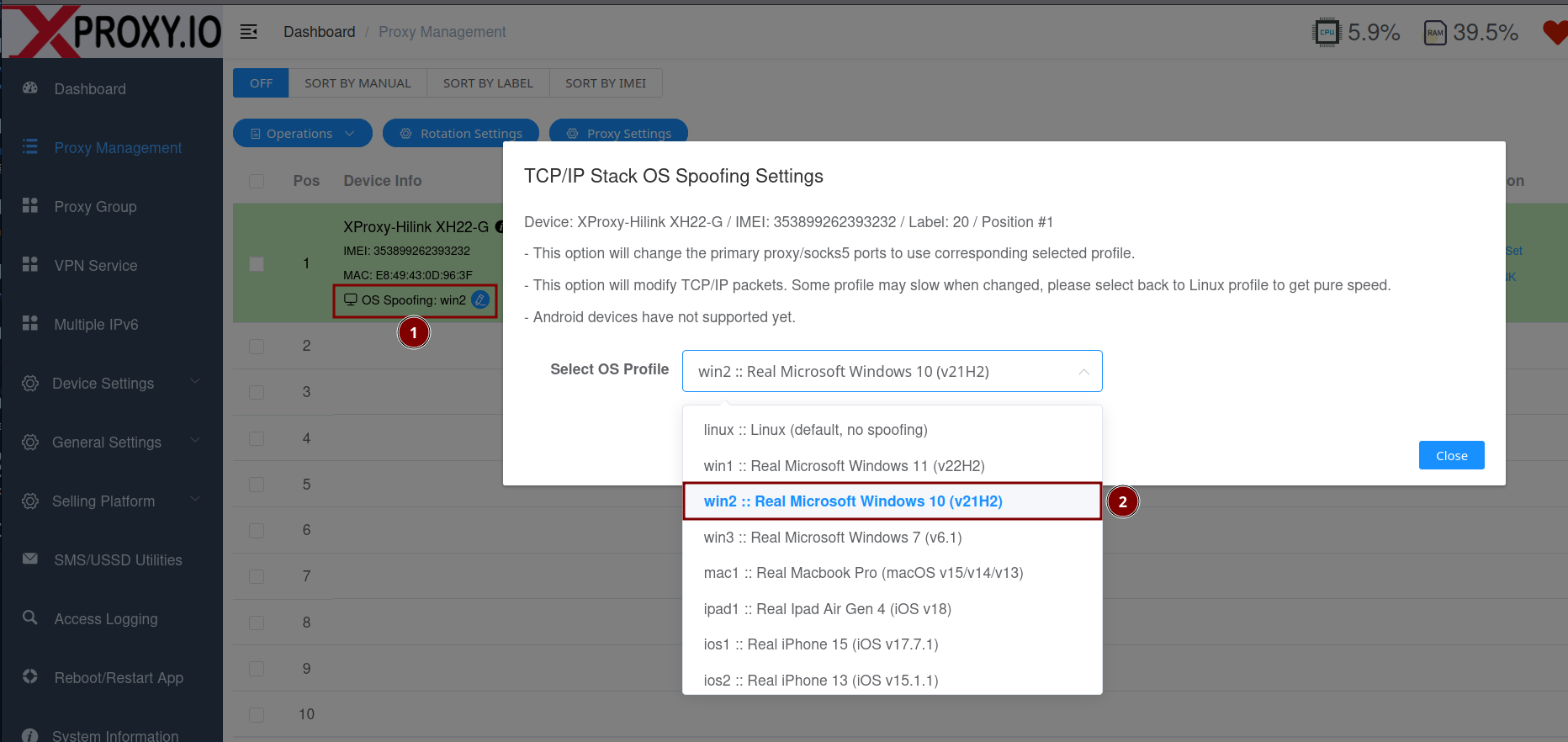
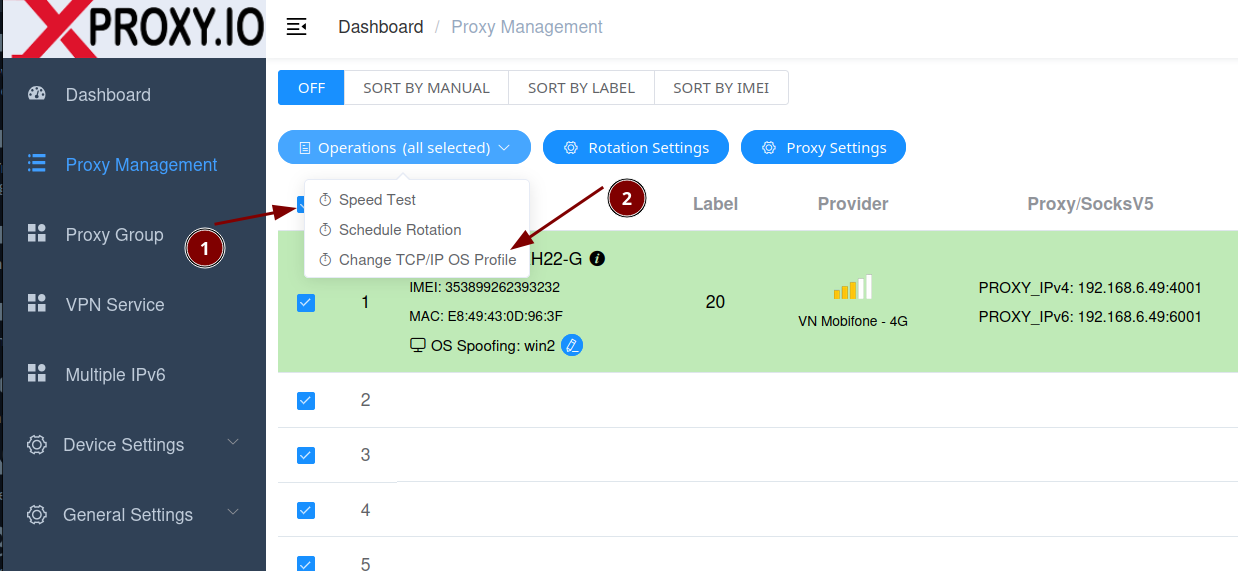
How to configure OS Spoofing in XProxy (GUI)
You can configure OS Spoofing per port or for multiple ports with a rule. Below are examples.
1) Configure OS Spoofing per individual port
Go to General Settings > Proxy Setting and open the Per-Port settings. Choose the OS you want to spoof (e.g., Windows).
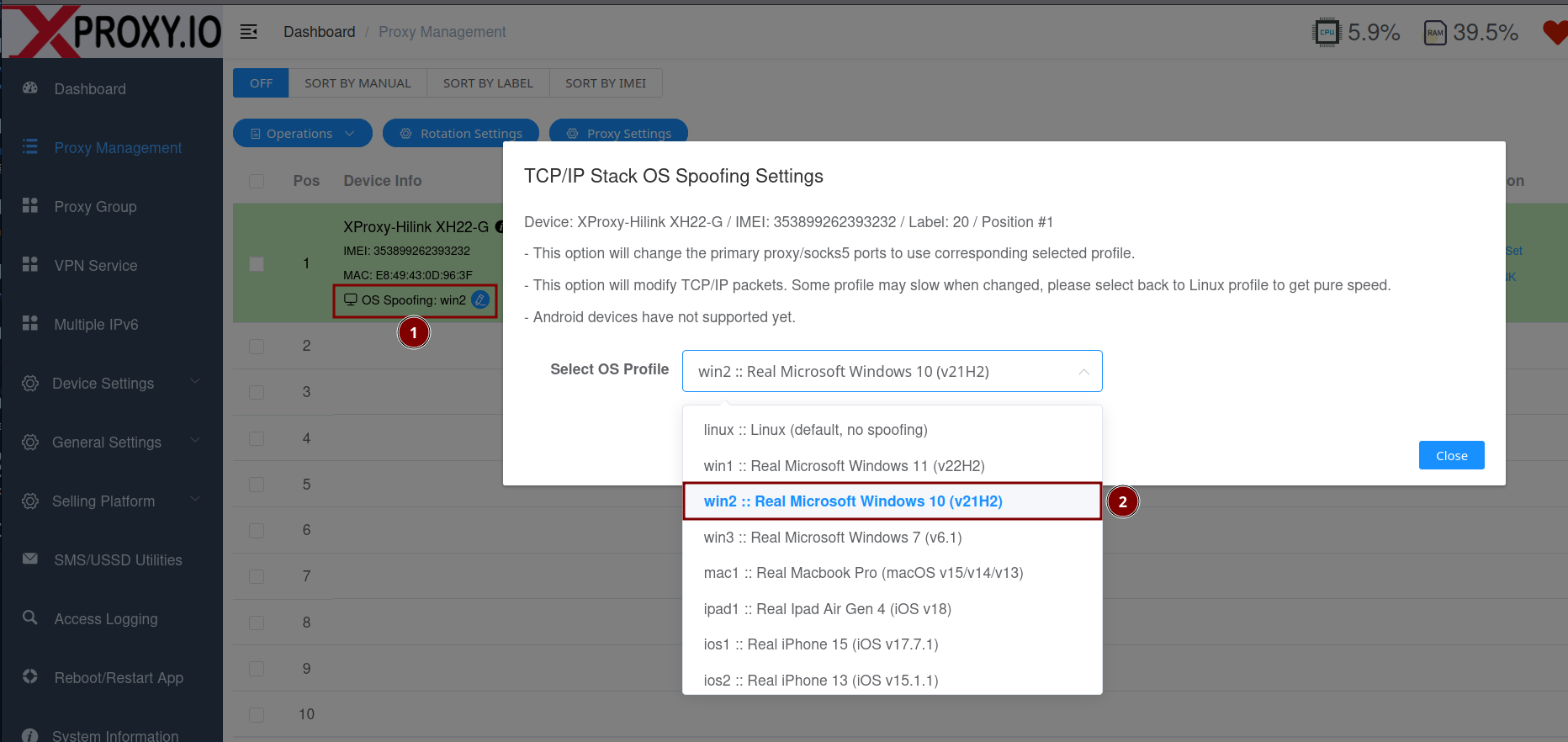
2) Configure OS Spoofing for multiple ports
Use the Multi-port rules area to apply the same OS spoof to a range of ports (useful when managing many proxies).
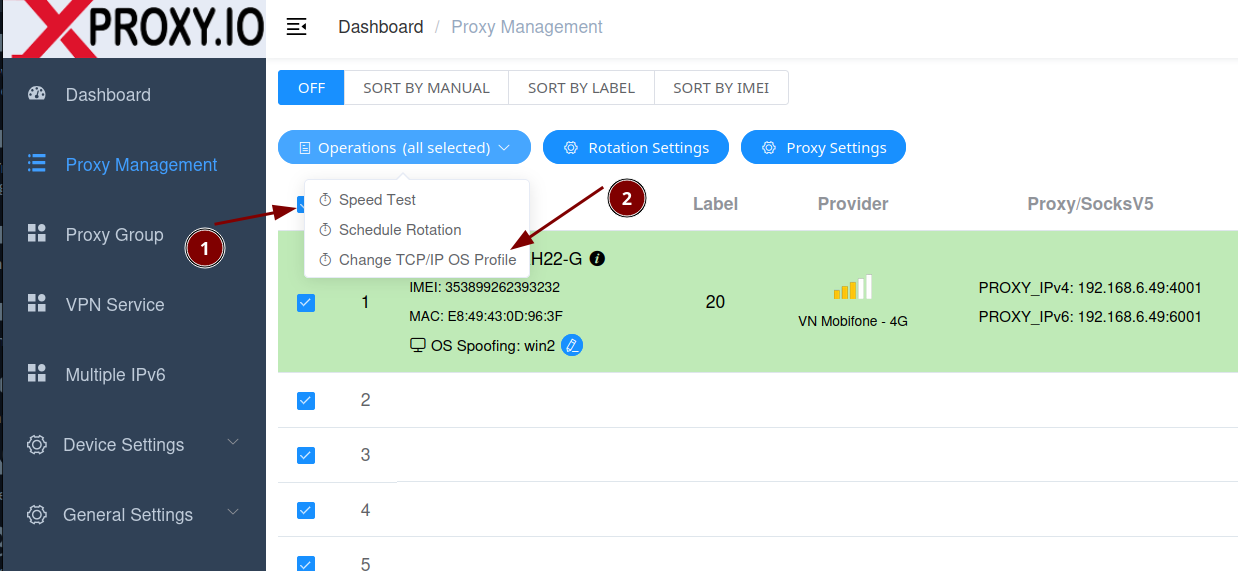
Tip: Match the spoofed OS with your browser profile’s OS (e.g., spoof Windows if your browser profile is Windows).
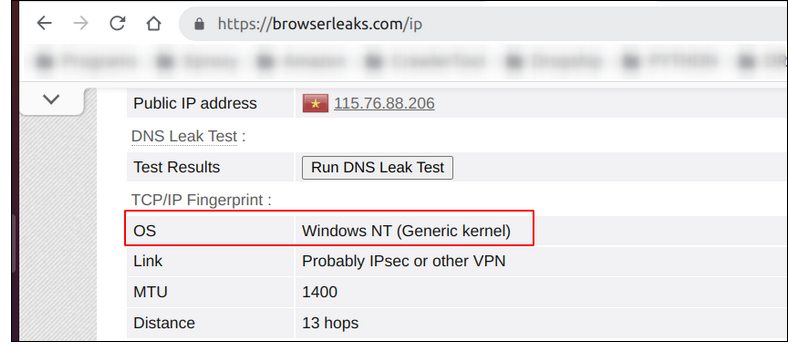
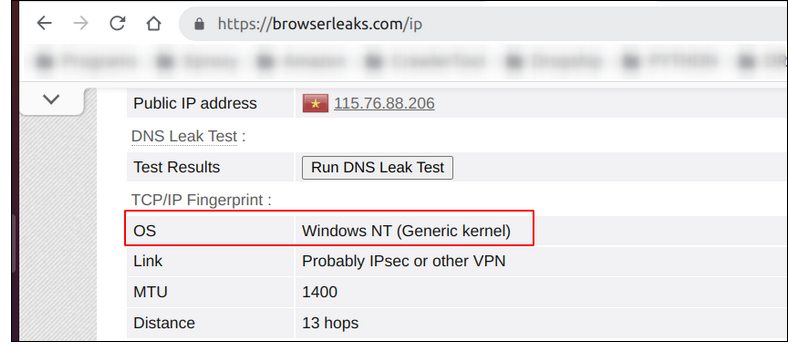
How to verify (Testing tools)
After enabling OS Spoofing, test with these tools:
Good practices
- Keep consistency: Browser profile OS, timezone, locale, fonts, and TCP/OS should tell the same story.
- Rotate carefully: Don’t change OS spoof too frequently for the same account/session.
Limitations and notes
- Not all network operators support (ISP NAT, firewalls, DPI/WAF, carrier-grade NAT) may normalize or strip TCP options (e.g., timestamps, SACK, window scale) or clamp MSS. This can override the spoofed signature on certain routes.
- Performance: Because packets may be inspected/rewritten (e.g., MSS clamping, option adjustments), you may see slight throughput/latency changes depending on OS profile and network path.
FAQ
No. Your browser/User-Agent stays the same. OS Spoofing aligns the TCP/IP signature at the proxy layer with your browser OS.
Choose the OS that matches your browser profile (most users pick Windows for desktop profiles).
Some may, because they check many signals. OS Spoofing is one important piece to reduce mismatches.
Some networks insert devices that normalize TCP: carrier‑grade NAT, firewalls/DPI, or upstream proxies. They can rewrite TTL, clamp MSS, drop or modify TCP options (timestamps, SACK, window scale), or use SYN cookies. When this happens, the path’s signature may look generic or Linux‑like regardless of your setting. Solution: try another ISP/APN/ASN or avoid extra VPN layers.
Linux (default), Windows, iOS, macOS, and Android. Choose the one that matches your browser or emulator profile for consistency.
TCP OS Spoofing is available starting from the Premium plan.
Using an actual Android phone/tablet as the proxy device (instead of a USB 4G/4G dongle modem) is not supported. However, choosing Android as the TCP/IP OS fingerprint is supported so the proxy can mimic Android when you use an Android browser profile or an emulator.
Potentially a little. Packet inspection and MSS/option adjustments can introduce minor overhead. The effect varies by profile and network conditions.